Elastic SIEM and SIRP – Unified Security Analysis, Enrichment, and Response
May 24, 2021
SOAR Use Case – Ransomware Attack
June 11, 2021SGBox and SIRP - Fusion of Next-Generation SIEM and SOAR

How does one choose from the unlimited reservoir of security solutions, tools, and technologies available to security teams? For security operations, nothing can beat the combination of a SOAR and SIEM platform.
SGBox offers a holistic approach to SIEM solutions with the ability to adapt to organizational requirements. Analysis of logs, vulnerability scans, and system monitoring are some of the added benefits that make SGBox the perfect choice for integration with SIRP.
A SOAR platform extends the efficiency, robustness, and response that SIEM alone cannot provide. SIRP SOAR (Security Orchestration, Automation and Response) solution integrates with SGBox to manage and enhance incidence response, alert correlation, and orchestrate and automate the repetitive and mundane tasks that delay security operations.
SOAR with SIEM together provide a comprehensive solution that creates an efficient, affordable, and successful plan for organizations; SIRP maximizes security analysts' efficiency while minimizing the response time, and this is made possible after alerts are taken into the SOAR platform through SGBox via the ingestion module.
Integration Features
- SIRP’s coalescence with SGBox ensures that no alerts go unnoticed.
- It escalates the consistency and standards of practices and procedures of the SOC team.
- Through SIRP, automated playbooks are triggered that make sure that the appropriate steps for investigation and response are taken.
- Alert enrichment also happens accurately and efficiently, also enhancing the containment or remediation time.
- For each event, an apt balance between human actions and automation is struck.
Challenges
A SIEM solution ingests large amounts of security data from multiple sources. The alerts are plenty, including false positives, and take up most of the time of a SOC analyst. The phrase “too much of a good thing” also applies here as alert fatigue takes off the security analysts. The number of security alerts being generated is insurmountable, true positive alerts get mixed with false positives, detection and response time increases, resources and tools are exhausted, and many alerts go unnoticed.
Solution
Employing SIRP’s SOAR platform enables security teams to process alerts from SGBox SIEM at a faster pace which enables them to reduce response time from hours to a few minutes. Various workflows and playbooks are available in the SIRP platform for investigating and responding to different alerts and events generated by SGBox. Not only does this considerably reduce alert fatigue and workload, but it also decreases time to respond and reduces the overall risk to the organization.
Use Case 1: Alert Aggregation and Investigation
The security alerts triggered by SGBox are ingested into SIRP can be processed manually, semi-automatically, or fully automatically by security teams. Workflows and playbooks are configured to process the alerts based on their type. Enrichment playbooks enrich the alerts by fusing in the information from different sources.
Use Case 2: Handling a Ransomware Attack
One of the most important use cases for SOC includes ransomware attack response. When a ransomware alert is ingested from the SGBox to SIRP, a case is automatically opened and assigned to an analyst for investigation. The affected host and user information are gathered and analyzed for any past related events. Once initial triage is completed, SIRP can then initiate the mitigation and containment actions to determine the extent of the attack, assess its aftermath, and initiate the response and remediation playbook.
Below is an example of a Playbook that can be executed from SIRP.
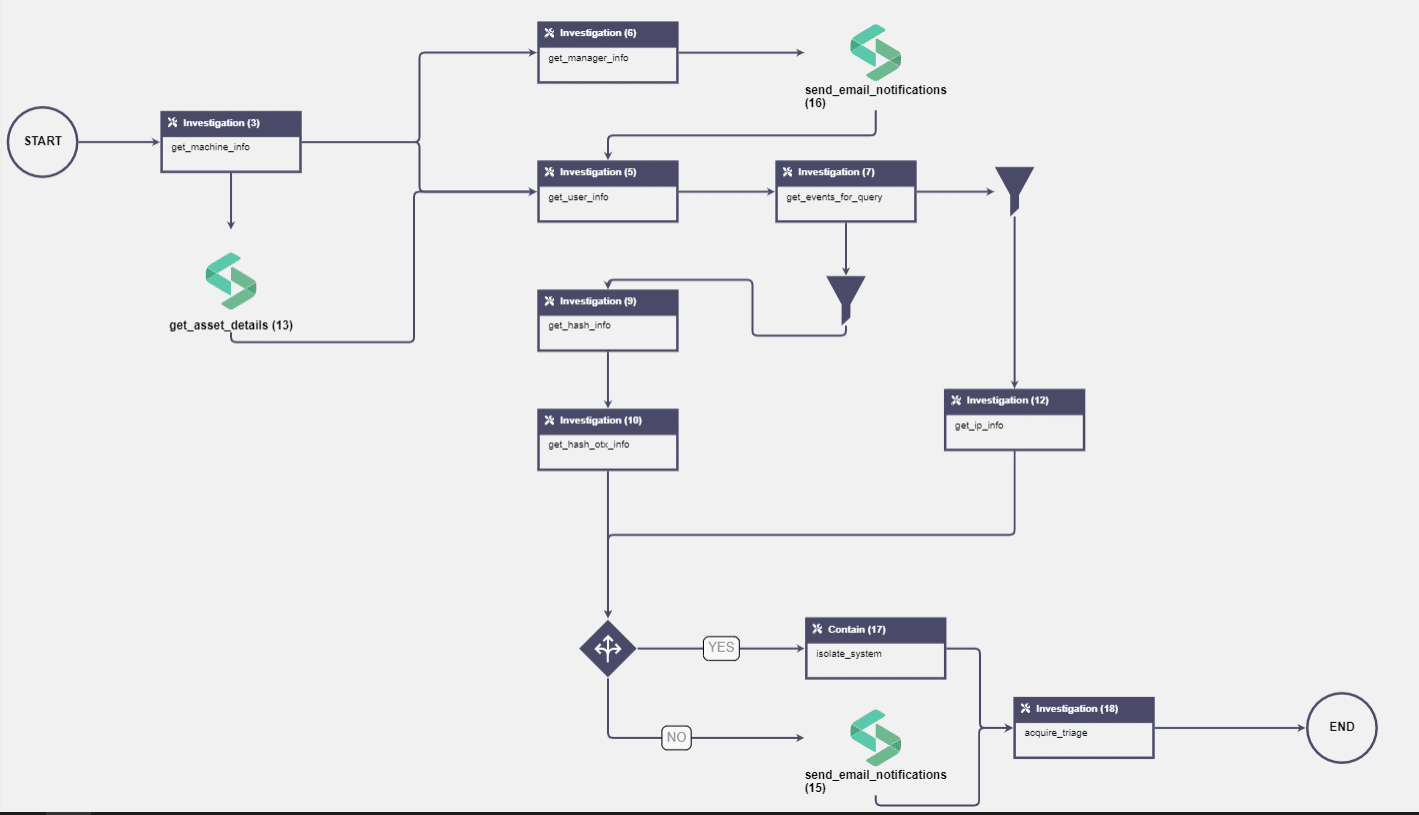
Once SIRP gets alerts from SGBOX via its ingestion module, assuming it is a ransomware alert containing workstation, IP address, and user information in the payload, the above playbook gets executed automatically with the following actions:
- Get Machine information from EDR.
- Get asset detail from SIRP Using username artifact from the evidence, run actions to get User information and User's Manager info using LDAP query.
- Taking action to email the user's manager informing them regarding Ransomware Alert on the system.
- Using SGBox get events action to return the events for the last hour from the machine’s IP address.
- Filter out Malware Hash and Destination IP information from the returned events.
- Action to check Hash and IP information using VirusTotal integration.
- Taking a Decision if the IP or Hash is in the ransomware category and has a 10+ threat score on VT.
- IF Yes, Isolate the system on the EDR tool.
- IF No, Email to L2 analyst and Custodian to investigate further.
- Also, take triage in the end to ensure further investigation by the analysts.
Benefits
- High-performance data collection and real-time analysis.
- Unlimited horizontal scalability and innovative user experience.
- Reduced response and mitigation time and a considerable decrease in alert fatigue.
- Actively hunt for cyberthreats and manage use cases.
